KGpg(签名、加密)
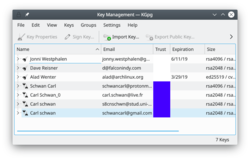 |
KGpg 为gpg命令提供了图形界面 |
GnuPG加密和解密你的邮件和选定的文件。完成这样的操作需要很多的命令选项。有了 KGpg 忧虑就可以消除了 - 你不再需要记住任何命令。KGpg帮你建立和管理你密钥,导入和导出密钥,查看密钥签名,信任等级和有效期。实际上差不多所有你需要做的事情KGpg都覆盖到了。同时也提供向导帮助你建立你的密钥。
KGpg 集成Konqueror 和Dolphin里, 这2个程序的右键关联菜单允许你选择签名和不签名情况下加密文件。
 |
 |
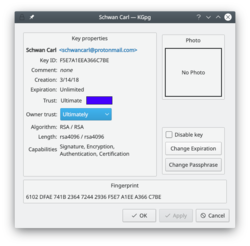
Extending the life of your keys
As you can see in the image above, you can extend the life of your keys using the button. Simply choose the new date from the popup calendar. To do this, however, you must have access to the private key and its pass-phrase. Without them you can do nothing.
Change your passphrase
Should you suspect your passphrase is compromised, you can change this also from the Key Properties dialogue. The button is below .
Revoking a key
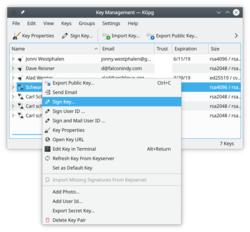
If you lose your private key or think it has been compromised in some way you need to revoke it. To reliably render a key unusable you need to revoke it. Revoking is done by adding a special revocation signature to the key.
The revocation signature can be created together with the key. In this case it is stored in a separate file. This file can later be imported into the keyring and is then attached to the key rendering it unusable.
If you have not created such a detached revocation on key creation you can
create such a revocation signature at any time choosing , optionally importing it to your keyring immediately.
这份 完整的说明手册 有助于你了解每个细节。
要是你没能力现实的验证联系人的身份,你应该读读密钥签名部分了解本地签名的益处。
Tutorials
- Verify GPG signatures with KGpg inside Dolphin (Source Peertube instance: peertube.mastodon.host)



