KGpg/es: Difference between revisions
Updating to match new version of source page |
Updating to match new version of source page |
||
| Line 20: | Line 20: | ||
== Change your passphrase == | == Change your passphrase == | ||
Should you suspect your passphrase is compromised, you can change this also from the Key Properties dialogue. The <menuchoice>Change Passphrase</menuchoice> button is below <menuchoice>Change Expiration</menuchoice>. | Should you suspect your passphrase is compromised, you can change this also from the '''Key Properties''' dialogue. The <menuchoice>Change Passphrase</menuchoice> button is below <menuchoice>Change Expiration</menuchoice>. | ||
== Revoking a key == | == Revoking a key == | ||
| Line 28: | Line 28: | ||
The revocation signature can be created together with the key. In this | The revocation signature can be created together with the key. In this | ||
case it is stored in a separate file. This file can later be imported into | case it is stored in a separate file. This file can later be imported into | ||
the keyring and is then attached to the key rendering it unusable. {{Warning|1=Please | the keyring and is then attached to the key rendering it unusable. | ||
note that to import this signature to the key no password is required. | |||
Therefore you should store this revokation signature in a safe place, | {{Warning|1=Please note that to import this signature to the key no password is required. Therefore you should store this revokation signature in a safe place, usually one that is different from you key pair. It is a good advise to use a place that is detached from your computer, either copy it to an external storage device like an USB stick or print it out.}} | ||
usually one that is different from you key pair. It is a good advise to | |||
use a place that is detached from your computer, either copy it to an | |||
external storage device like an USB stick or print it out.}} | |||
If you have not created such a detached revocation on key creation you can | If you have not created such a detached revocation on key creation you can | ||
Revision as of 16:53, 14 September 2011
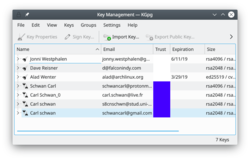 |
KGpg es una interfaz gráfica para gpg |
GnuPG cifra y descifra tus correos y archivos seleccionados, aunque se necesitan muchas opciones en la línea de órdenes para conseguirlo. Con KGpg la ansiedad se quita puesto que no tienes que recordar ninguna opción. KGpg puede ayudarte a configurar y gestionar tus claves, importar y exportar claves, ver las firmas de las claves, estados de confianza y fechas de caducidad. De hecho, prácticamente todo lo que necesitas se puede hacer desde KGpg. Además dispone de un asistente para ayudarte en la configuración de tus claves.
KGpg está integrado en Konqueror y Dolphin, donde un menú contextual te permite cifrar un archivo, tanto firmado con sin firmar.
 |
 |
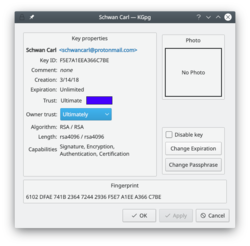
Extending the life of your keys
As you can see in the image above, you can extend the life of your keys using the button. Simply choose the new date from the popup calendar. To do this, however, you must have access to the private key and its pass-phrase. Without them you can do nothing.
Change your passphrase
Should you suspect your passphrase is compromised, you can change this also from the Key Properties dialogue. The button is below .
Revoking a key
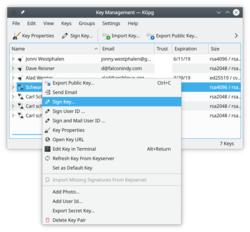
If you lose your private key or think it has been compromised in some way you need to revoke it. To reliably render a key unusable you need to revoke it. Revoking is done by adding a special revocation signature to the key.
The revocation signature can be created together with the key. In this case it is stored in a separate file. This file can later be imported into the keyring and is then attached to the key rendering it unusable.
If you have not created such a detached revocation on key creation you can
create such a revocation signature at any time choosing , optionally importing it to your keyring immediately.

Tip

Tip
Un manual totalmente ilustrado te ayudará con cada detalle.
Si no estás en condiciones de verificar físicamente la identidad de tus contactos deberías leer la sección de cifrado de claves que explica los beneficios del cifrado local.


