KGpg: Difference between revisions
No edit summary |
No edit summary |
||
| Line 1: | Line 1: | ||
<languages /> | <languages /> | ||
<translate> | <translate> | ||
__TOC__ | |||
<!--T:1--> | <!--T:1--> | ||
{|style="text-align:center" | {|style="text-align:center" | ||
Revision as of 15:07, 14 September 2011
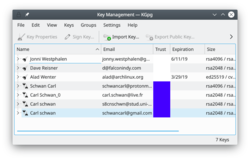 |
KGpg provides a graphical interface to gpg's commands |
GnuPG encrypts and decrypts your mail and selected files. There are many command-line options to achieve this. With KGpg the anxiety is removed - you don't have to remember any commands. KGpg can help you set up and manage your keys, import and export keys, view key signatures, trust status and expiry dates. In fact just about everything you need to do is covered by KGpg. A wizard is provided to help you set up your keys.
KGpg is integrated into Konqueror and Dolphin, where a context menu allows you to choose to encrypt a file, with or without signing.
 |
 |
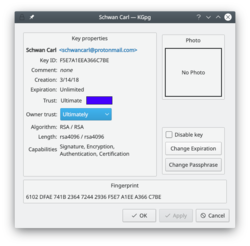
Extending the life of your keys
As you can see in the image above, you can extend the life of your keys using the button. Simply choose the new date from the popup calendar. To do this, however, you must have access to the private key and its pass-phrase. Without them you can do nothing.
Change your pass-phrase
Should you suspect your pass-phrase is compromised, you can change this also from the Key Properties dialogue. The button is below .
Revoking a key
If you lose your private key or think it has been compromised in some way you need to revoke it. To reliably render a key unusable you need to revoke it. Revoking is done by adding a special revocation signature to the key.
The revocation signature can be created together with the key. In this case it is stored in a separate file. This file can later be imported into
the keyring and is then attached to the key rendering it unusable.
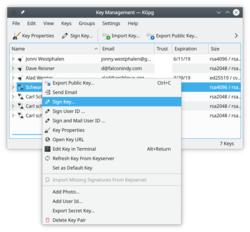
If you have not created such a detached revocation on key creation you can
create such a revocation signature at any time choosing , optionally importing it to your keyring immediately.

Tip

Tip
A full illustrated manual helps you through every detail.
If you are not in a position to physically verify the identity of your contacts you should especially read the key-signing section which explains the benefits of local-signing.


